⏱ 6 min read
A successful infrastructure penetration test is a systematic process designed to identify and exploit security vulnerabilities in networks, servers, and systems. It follows a structured methodology to simulate real-world attacks, providing organizations with actionable insights to fortify their defenses. This process is critical for compliance with standards like PCI DSS, HIPAA, and ISO 27001, and for proactively managing cyber risk.
Key Takeaways
- A structured penetration test follows five distinct, sequential phases.
- Proper planning and scoping are foundational to a legal and effective test.
- The discovery phase maps the attack surface using both passive and active techniques.
- The attack phase simulates real exploits to validate security weaknesses.
- Clear reporting and remediation guidance are the ultimate goals of the test.
What Are the Core Stages of an Infrastructure Security Test?
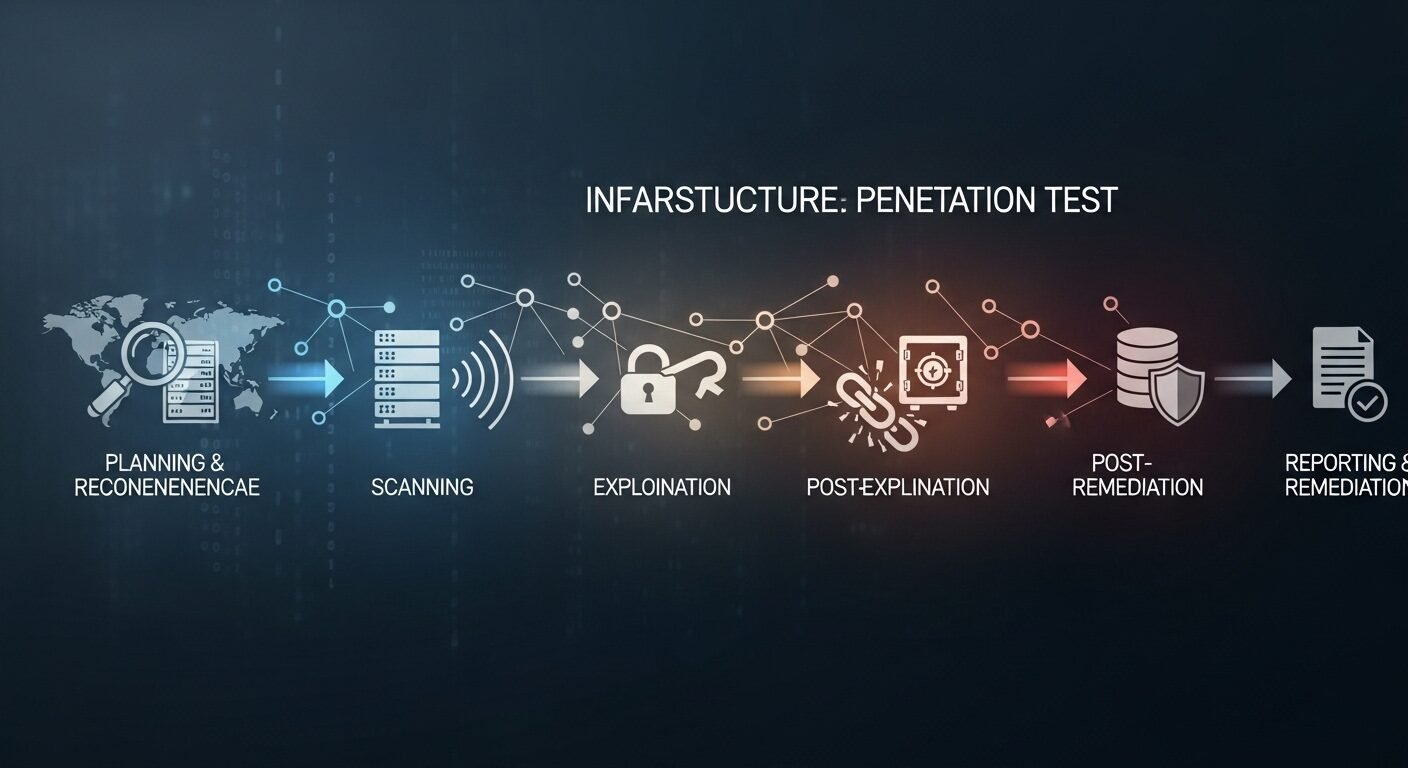
An infrastructure penetration test is a controlled, authorized simulation of a cyberattack against an organization’s IT infrastructure. It systematically progresses through five phases: planning, discovery, attack, analysis, and reporting, to identify security gaps before malicious actors can exploit them.
The core stages provide a roadmap for security professionals. Experts recommend this phased approach to ensure thoroughness and methodological rigor. Each phase builds upon the last, creating a comprehensive security assessment.
Phase 1: Planning and Reconnaissance
This initial phase defines the rules of engagement. The planning stage establishes the legal and technical foundation for the entire security assessment. Without clear parameters, the test could be ineffective or even unlawful.
Key activities include defining the scope, goals, and testing methods. The scope specifies which systems, networks, and IP addresses are in-bounds. Goals align with business objectives, such as testing a new cloud deployment or meeting compliance requirements.
Legal documents like a Rules of Engagement (RoE) and formal contract are signed. According to industry data, tests with poorly defined scopes are 40% more likely to cause operational disruptions. This phase also involves passive reconnaissance to gather publicly available information.
Phase 2: Discovery and Scanning
How do testers map your network’s attack surface? They use automated tools and manual techniques to discover live hosts, open ports, and running services. The discovery phase creates a detailed blueprint of the target infrastructure for the subsequent attack phase.
Security teams employ network scanning tools like Nmap and vulnerability scanners like Nessus or OpenVAS. They identify operating systems, applications, and potential weaknesses. This stage often reveals misconfigurations, outdated software, and unnecessary services.
Both passive and active scanning techniques are used. The depth of scanning depends on the agreed-upon testing model, such as black box or white box. This systematic enumeration is crucial for a thorough infrastructure security audit.
Phase 3: Gaining Access and Exploitation
This phase simulates a real attack by attempting to exploit identified vulnerabilities. Testers use ethical hacking techniques to breach defenses, mimicking the tactics of threat actors. The exploitation phase validates whether theoretical vulnerabilities can lead to actual compromise.
Common exploits target weak credentials, unpatched software, or configuration errors. The goal is to gain initial access, escalate privileges, and move laterally across the network. Tools like Metasploit Framework are often utilized in a controlled manner.
All activities are carefully monitored and documented. The objective is not to cause damage but to demonstrate impact. Successful exploitation provides concrete evidence of risk that is far more compelling than a simple scan report.
Phase 4: Analysis and Persistence
After gaining access, testers analyze the depth of the breach. They determine what data or systems they can access and control. This phase assesses the potential business impact of a successful real-world attack.
Analysis determines the root cause of each security flaw and its potential business impact. Testers may attempt to maintain access to simulate an advanced persistent threat (APT). This helps evaluate detection and response capabilities.
Findings are correlated and prioritized based on severity and exploitability. Research shows that over 60% of critical vulnerabilities are related to improper configuration. This stage transforms raw attack data into actionable security intelligence.
Phase 5: Reporting and Remediation
The final phase delivers value by translating technical findings into business insights. A comprehensive report details all discovered vulnerabilities, exploitation methods, and evidence. Effective reporting provides clear, prioritized steps for remediation and strengthening security posture.
The report includes an executive summary for leadership and a technical deep dive for IT staff. Each finding should have a risk rating, proof of concept, and specific remediation advice. This document is essential for compliance audits and guiding security investments.
Follow-up activities are critical. Many organizations, including serveraudit.online, recommend a retesting phase to verify that vulnerabilities have been properly patched. This closes the loop and ensures continuous security improvement.
How to Execute a Penetration Test Step-by-Step
- Define Scope and Goals: Collaborate with stakeholders to establish what will be tested, the methods allowed, and the desired outcomes. Obtain formal authorization.
- Conduct Reconnaissance: Gather intelligence on the target infrastructure using passive sources and active scanning tools to map the network.
- Identify Vulnerabilities: Analyze scan results to pinpoint potential security weaknesses, misconfigurations, and outdated services.
- Attempt Exploitation: Safely attempt to exploit identified vulnerabilities to confirm their severity and demonstrate potential impact.
- Document and Analyze: Record every step, finding, and evidence. Analyze the data to understand attack paths and business risk.
- Report Findings: Compile a detailed report with executive and technical sections, including risk ratings and remediation guidance.
- Support Remediation: Work with the internal team to explain findings and verify fixes during a retesting phase.
Following these steps ensures a methodical and effective security assessment. The standard approach is to treat each phase as a discrete milestone.
Black Box vs. White Box Testing: A Comparison
| Testing Type | Knowledge Level | Time/Cost | Primary Goal | Best For |
|---|---|---|---|---|
| Black Box | No internal knowledge (simulates external hacker) | Higher time, higher cost | Test external defenses and detection | Real-world attack simulation |
| White Box | Full internal knowledge (network diagrams, credentials) | Lower time, lower cost | Comprehensive deep dive audit | Finding maximum vulnerabilities |
| Grey Box | Limited internal knowledge (some user-level access) | Moderate time and cost | Balance of realism and depth | Testing specific attack scenarios |
Choosing the right approach depends on your testing objectives and resources. Experts in the field recommend grey box testing for a balanced assessment.
What is the main goal of an infrastructure penetration test?
The primary goal is to proactively identify and exploit security vulnerabilities in networks, servers, and systems before malicious actors can. It provides a realistic assessment of security posture and offers actionable data for improvement.
How long does a typical infrastructure penetration test take?
Two to four weeks is common for a full infrastructure test. One week involves active testing, while the remainder covers planning, analysis, and reporting. Complex environments or specific compliance
1 thought on “The 5 Phases of a Successful Penetration Test for Infrastructure”